CSIRT GOV Poland – Computer Security Incident Response Team recently published a very interesting and insightful report on the state of cybersecurity in Poland in 2024.
Publication date: August 26, 2025
What is CSIRT GOV and what is its legislative environment
The Polish Computer Security Incident Response Team (CSIRT GOV), led by the Head of the Internal Security Agency, serves as the national CSIRT. The CSIRT GOV is responsible for coordinating the response process to computer incidents occurring in the area specified in Article 26, Section 7 of the Act of 5 July 2018 on the National Cybersecurity System.
The first European cybersecurity regulation is Directive (EU) 2016/1148 of the European Parliament and of the Council of 6 July 2016 concerning measures for a high common level of security of network and information systems across the European Union, known as the Network and Information System Directive (NIS). The directive imposes numerous obligations on Member States, primarily involving the establishment of appropriate institutions, the adoption of a national strategy for the security of network and information systems, and the introduction of cooperation mechanisms. This directive established a network of computer security incident response teams (CSIRTs).
The Act on the National Cybersecurity System, adopted by the Polish legislator on 28 August 2018, serves to achieve the objectives set out in the NIS Directive. Pursuant to Article 1 of the Act on the National Cybersecurity System, the act specifies: the organization of the national cybersecurity system and the tasks and responsibilities of the entities comprising this system, the method of exercising supervision and control over the application of the provisions of the act, as well as the scope of the Cybersecurity Strategy of the Republic of Poland.
The legislator, in principle, decided to create three teams:
• CSIRT GOV – Computer Security Incident Response Team operating at the national level, led by the Head of the Internal Security Agency,
• CSIRT MON – Computer Security Incident Response Team operating at the national level, led by the Minister of National Defence and
• CSIRT NASK – Computer Security Incident Response Team operating at the national level, led by the Scientific and Academic Computer Network – National Research Institute (Article 2 of the Act on the National Cybersecurity System).
The competence of CSIRT GOV and CSIRT MON is defined in Article 27 of the Act on the national cybersecurity system as follows: “CSIRT GOV is competent in the scope of incidents related to events of a terrorist nature, referred to in Article 2 point 7 of the Act of June 10, 2016 on counter-terrorist activities (Journal of Laws of 2024, item 92); CSIRT MON is competent in the scope of incidents related to events of a terrorist nature, referred to in Article 5 paragraph 1 point 2a of the Act of June 9, 2006 on the Military Counterintelligence Service and the Military Intelligence Service (Journal of Laws of 2023, items 81, 1834 and 1860).
One of the basic tasks of CSIRT NASK is to recognize, prevent, and detect threats to the security of public administration bodies’ ICT systems or ICT systems and networks covered by the uniform list of facilities, installations, devices, and services constituting critical infrastructure, as well as ICT systems of owners and holders of critical infrastructure facilities, installations, or devices, referred to in Art. 5b paragraph 7 item 1 of the Act of 26 April 2007 on Crisis Management.
CSIRT GOV Annual Report
CSIRT GOV has just published a report on the state of cybersecurity in 2024. The document comprehensively presents statistics on the number and types of incidents and threats, comparing them with data from previous years. It presents the most significant threats and undesirable cyber activity targeting the IT infrastructure of public authorities, critical infrastructure operators, and entities providing essential services. The report is based on an analysis of IT security incidents reported and identified by CSIRT GOV, data obtained using systems enabling autonomous threat detection, and information obtained from the Team’s active activities. The study also includes analyses of the changing cybersecurity landscape, significant trends, and potential security weaknesses.
The Report highlights at least two interconnected circumstances that seem to force reflection on the significance of cybersecurity threats and the systems designed to eliminate or mitigate them. On the one hand, it highlights the technological trend that is increasingly permeating our lives with each passing moment. The result is rapid digitization, which is taking place through the transfer of increasing amounts of data relating to citizens, public services, communications, and finances to the digital sphere. The undeniable convenience of such applications also means that cyberspace can be increasingly effectively used to launch attacks on a scale that seriously threatens the security of the state and its citizens.
The second factor is the geopolitical environment and context. On March 1, 2024, the CRP alert level for cyber threats was lowered from the previously applicable CHARLIE-CRP, the third of four alert levels, to the currently applicable BRAVO-CRP, the second alert level. This, however, means that we are still dealing with a state of heightened threat in Polish cyberspace, despite a slight reduction in the intensity of this threat. The changing landscape of conflicts between states was also highlighted. Unlike in the past, conflicts take the form of not only kinetic clashes but also involve the use of a full spectrum of tools, including those extending into cyberspace. Ultimately, they most often take the form of “hybrid operations or wars,” which can complement military actions, serve as an alternative, or serve as a precursor to a kinetic strike. For this reason, it is important to consider the broader context of emerging incidents.
2024 was a year of dual elections: local government and the European Parliament, which each time requires vigilance on the part of bodies like CSIRT GOV due to the much more widespread threat of disinformation. It is also necessary to ensure the proper functioning of the IT systems used to conduct elections, with citizens’ trust in the democratic process ultimately at stake.
CSIRT GOV Coordinated Incident Statistics
In 2024, a decrease in reports registered by the CSIRT GOV Team regarding potential ICT incidents was observed. Of the 17,439 reports, 3,991 were classified as actual ICT security incidents. In 2022, 26,753 reports and 4,959 incidents were recorded, followed by 19,888 reports and 4,676 incidents in 2023. These statistics do not include reports from the ARAKIS GOV system. The lack of data from ARAKIS, a dedicated, distributed early warning system for ICT threats occurring at the interface between internal networks and the internet, may be due to the need to separate these statistics, which will be discussed later in this article.
There are no significant differences in registered reports and incidents between individual quarters in 2024. However, the highest number of incidents was recorded in the second quarter, which was related to an increase in resource unavailability and the publication of sensitive data in open sources, i.e., leaks.
The CSIRT GOV team indicates that the factors that led to the decrease in incidents include: 1) proactive activities conducted by CSIRT GOV to increase user awareness through training; 2) reporting on identified vulnerabilities within the area of competence; 3) ongoing issuance of CSIRT GOV recommendations – appropriate to the CRP threat level; 4) regular distribution of compromise indicators for monitored campaigns; 5) periodic security assessments of IT systems; 6) the institution’s implementation of security solutions that mitigate attacks in their early stages.
Division of incidents reported by entities of the national cybersecurity system into categories
The highest percentage of recorded incidents, and the most significant increase, occurred in the Vulnerability category. The numbers for incidents in this category are as follows: 1,105 incidents compared to 993 in the previous year. This category refers to security vulnerabilities identified by the CSIRT GOV Team resulting from the vulnerability of resources and services accessible via the Internet by entities under the CSIRT GOV’s jurisdiction.
Vulnerability refers to a weakness in an IT system, e.g., in procedures, design, implementation, or internal controls, that can be exploited for unauthorized access, data destruction or disclosure, data alteration, system weakening, etc.
The next category is Publication. In this regard, there was a decrease in such incidents from 1,052 in 2023 to 902 in 2024. Publication refers to the disclosure of sensitive data through leaks, including login credentials for electronic services, private PGP keys, or information about the specifications of an institution’s IT infrastructure.
Among the activities recorded in the Social Engineering category, the GOV CSIRT Team identified phishing emails aimed at obtaining login credentials for electronic services or other sensitive data, infecting them with malware, or extorting funds. There was a noticeable and significant decline in incidents in this category. In 2024, 815 such incidents were recorded, compared to 1,362 in the previous year. A decrease was also noted in the
Unavailability category, which includes DoS / DDoS attacks (773 incidents in 2023 and 478 in 2024). The remaining, smaller categories, to which a similar number of incidents were assigned as in 2023, are Attack (325 in 2023 to 261 in 2024) – events recorded in this category included attempts to break security by exploiting vulnerabilities, bruteforce attacks, compromise of accounts and systems, and exfiltration of data from adopted IT resources, Cascade (235 incidents in 2024, category not presented in previous years) – referring to reports and incidents related to terrorist events, based on Article 27 of the Act on the National Cybersecurity System. These include all activities aimed at minimizing terrorist threats undertaken by CSIRT GOV in coordinating incident management.
Scanning, or reconnaissance of IT infrastructure to identify vulnerable systems and services, is a category that has seen an increase compared to the previous year (108 incidents in 2024, compared to 101 in 2023). This category includes incidents indicating the possibility of preparing offensive actions aimed at breaching security or compromising the availability of services. The two smallest incidents in terms of number of incidents are Content (53 incidents in 2023, 56 in 2024) and Virus (37 incidents in 2023, 31 in 2024). The former concerns incidents violating broadly understood public goods, such as information damaging the image of state entities or publishing disinformation content. This primarily includes the mass use of the image of persons holding leadership positions in the state, for example, to extort funds from citizens. The Virus category classifies incidents involving malware identified on workstations, servers, and network devices.
The report also includes data on the number of incidents reported by entities within the national cybersecurity system in 2024, broken down by sector. According to this data, the largest number of incidents occurred in the Institutions and Critical Infrastructure Operators sectors. The next sectors in terms of the number of recorded incidents were: State Authority, Office, Ministry, Other, and Service.
Social engineering campaigns in 2024
Social engineering campaigns identified by CSIRT GOV in 2024 most often involve attempts to obtain confidential data, such as login credentials, by impersonating various institutions (phishing), while creating various fictitious scenarios to lend credibility to requests, such as a password reset via a hyperlink sent in an email that led to a fake website. Among the most interesting social engineering campaigns cited by CSIRT GOV in the Report was a phishing campaign involving the sending of messages from a compromised email address belonging to a district office, with a terse subject line and content intended to give the impression that it was part of prior arrangements or correspondence between the sender and recipient. The messages contained attachments named additional (02).docx.exe or additional (03).docx.exe, which contained the Agent Tesla Trojan malware.
Another social engineering campaign, based on a similar theme, also stands out. The goal was to infect recipients’ devices with malware. The sender impersonated PGNiG Obrót Detaliczny sp. z o. o. in the email. The email, titled “PGNiG – Request for Offer: Suwalki Project 2025/2026,” was intended to intrigue the recipient and persuade them to interact with the attachment. The attached archive, titled “PGNIG Request for Offer: Suwalki Project 20252026.gz,” contained a VBS file with the same name. Analysis conducted by the CSIRT GOV team revealed that the script was responsible for downloading malware classified as the GuLoader Trojan from the mobiera.ro domain.
Since the end of August 2024, the CSIRT GOV team has received information about a phishing campaign in which an adversary impersonates the Chancellery of the Prime Minister to obtain login credentials for banking portals (officially used as a login method for government e-services such as mObywatel and Trusted Profile). The website in question was located in the environment.odszkodowanie-gov.com domain. The website used the image of the Chancellery of the Prime Minister and the style of the official government website, which is used by the state administration within the gov.pl domain. The website displayed information about a supposed compensation that every household was entitled to in excess of PLN 400. To receive these funds, users had to authenticate using a bank of their choice. After selecting a financial institution from the list, the fake bank’s website loaded, displaying a login panel.
The most important trends in social engineering attacks in 2024 include: the use of compromised email accounts of local, provincial, national or international institutions, including the takeover of government email accounts (including those in the gov.pl domain), the use of QR codes instead of classic links, allowing the bypassing of automatic scanning of potentially malicious content by email security filters, signing documents using services such as DocuSign and encouraging the display of shared documents on real services such as Microsoft SharePoint or Google Drive, and the use of the image (e.g. logo) of Polish and European law enforcement agencies to intimidate the recipient into taking appropriate action.
The threat from sponsored and hacktivist groups
Threats stemming from sponsored groups are typically characterized by a high level of technical sophistication and sophistication. A key characteristic of these groups is remaining hidden while simultaneously ensuring access to compromised infrastructure. Due to its geopolitical location, Poland is particularly vulnerable to these threats, stemming primarily from the activity of adversaries supporting primarily Russian goals or narratives. Furthermore, in 2024, attacks attributed to hacktivist groups continued to be a constant feature of the cyberthreat landscape. Unlike sponsored groups, these groups intensively published information about their activities on social media to reach the widest possible audience and thus promote their ideological goals. These groups focused their activities on DDoS attacks aimed at disrupting the availability of services and websites, a continuation of the activities from 2022 and 2023. In 2024, a wide range of APT activity was recorded, with the dominant actor in the CRP being the APT group known as APT28, also known as Fancy Bear, which, according to some sources, was actually part of the Russian GRU. ATPs pose a serious threat to the Polish state. ATP28’s mission is primarily to conduct espionage operations, and its targets primarily include government and military institutions, international organizations, and strategic sectors of the economy. ATP activity was characterized by the use of advanced, multi-stage techniques aimed at obtaining credentials, installing malware, and providing persistent access to victim systems.
Example of an ATP28 attack using… Windows Calculator
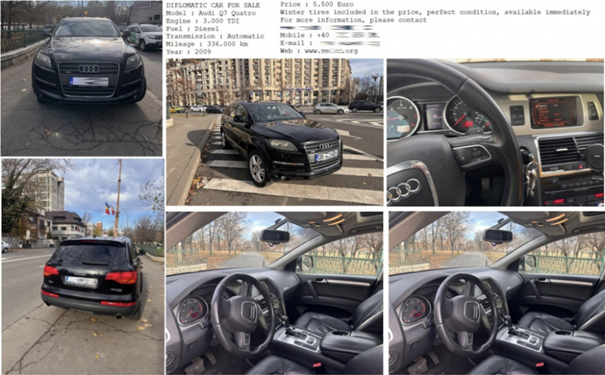
Perhaps the most spectacular attack involved the distribution of the HEADLACE malware. According to the report, the attack began with an email containing a malicious link, simulating an offer to sell a car from the diplomatic fleet. The email was sent from an email address in the bigmir.net domain, which indicated a Ukrainian email provider. The message encouraged users to open a link under the guise of an Audi car for sale, when in reality the link referred to a webhook.site website. The website’s script verified the value of the browser’s UserAgent header. If the victim was using a non-Windows system, a benign image was displayed; otherwise, a ZIP archive containing three files was downloaded to the victim’s computer: EXE, DLL, and BAT. The executable file had a double.jpg.exe extension to imitate a graphic file, as in previous campaigns. The image in question was a so-called decoy file:
Most interestingly, the file with the .jpg.exe extension was a copy of the authentic Windows Calculator application. However, the Windows Calculator was vulnerable to the so-called DLL Side-Loading technique. (Malware readily exploits the characteristics of dynamic link libraries ( .dll ). The fundamental characteristic of dll libraries is that they require a process to execute the code contained within them. This is where all the abuses in the form of injecting malicious .dll libraries into trusted program processes occur. If Windows or an installed application only checks the name of the .dll library to be loaded, without verifying the checksum or digital signature, it is possible to replace such a .dll library with a malicious one). The purpose of the library in question was to execute the last of the three files, a BAT script. As a result of executing the BAT file, a file with the .jpg20 extension was downloaded from a resource in the webhook [.] site domain using Microsoft Edge. This file was then transferred to another location, changing the file extension to .cmd using the script for execution. Following the attack, some artifacts were deleted to minimize the risk of detection. The final payload returned information from the victim’s workstation, including a list of files from the Desktop and Downloads folders, as well as the IP address.
What else is the ATP28 group responsible for?
ATP28 activity also included another type of phishing activity, involving impersonating email administrators and persuading users to provide their login credentials in a fake Outlook Web Access panel. In 2024, several such campaigns targeted government administrations, including password change panels in both Polish and English, as well as those designed to increase the size of email inboxes. This type of phishing is a classic method of obtaining sensitive data, and the effectiveness of the attack is related to the maturity of individual entities in terms of their cybersecurity measures, which are also within the actor’s area of interest.
Among the activities that most likely fit into the APT28 cluster of activity were password bruteforce attacks, spraying and credential stuffing email accounts and VPN services27 to gain access to email and other resources processed by employees of entities targeted by Russian-sounding APT groups. To conceal the attempted breach, the actor used access through anonymizing networks and residential proxies, using compromised network devices belonging to private users or small businesses, usually geolocated in the same country. In 2024, the actor also reportedly used the DCSync technique to mass replicate user login data within a domain controller, the so-called credential dump. This may result in ensuring the actor’s long-term access to the infrastructure by creating the so-called Golden Ticket -ui to carry out the Pass the Ticket attack. These activities are consistent with the group’s modus operandi, which, after gaining access to infrastructure, employs so-called living- off-the-land techniques, involving the use of available system tools to escalate privileges or exfiltrate data.
Hacktivists and Cybercrime
Following the outbreak of the war in Ukraine, numerous groups and collectives emerged, conducting a kind of guerrilla activity in cyberspace. The term “hacktivism” itself comes from a combination of the words “hack” and “activism,” and is—as the name suggests—the transference to cyberspace of the activities of activists fighting for various political or ideological goals. In the case of pro-Russian ” hacktivists ,” the motivation they present on social media is primarily support for Russian military actions and “punishing” NATO alliance members for their military support of Ukraine. The most well-known groups include Killnet , Anonymous Sudan (despite its name, it aligns with Russia’s narrative), Cyber Army of Russia Reborn , XAKNET, Solntsepek , UserSec , NoName057(16), Zarya , Beregini, and Z- Pentest. Their primary method of operation is DDoS attacks, usually technically unsophisticated but heavily publicized for propaganda purposes. In 2024, the CSIRT GOV team also recorded malicious activity targeting domestic entities, including attempted hacks into IIoT ( Industrial Internet of Things ) systems with remote access over the internet, including through HMI (Human-Machine Interface) panels. This is a new manifestation of hacktivist threats, which have somehow become a focus of interest for these groups. Attacks on such devices were often due to the lack of adequate remote access protection. These weaknesses were also noticed by hacktivist groups. These groups, taking advantage of online login panels, engaged in activities aimed at gaining unauthorized access, primarily through the use of default login credentials. This threat particularly affected facilities such as sewage treatment plants, water treatment plants, waste incineration plants, and facility management facilities.
In 2024, CSIRT GOV also noted cybercriminal activity, including Chinese groups belonging to the Quad7 botnet using vulnerable TP-Link devices. The botnet was used to anonymize attacks, including attempts to take over Microsoft 365 accounts. The UAC-0050 ( DaVinci Group) group also operated, conducting widespread phishing campaigns, including in Poland. Unlike APT groups, which strive to remain hidden and attack precisely selected targets, the DaVinci Group’s modus operandi is different. The group prefers broad attacks and pays little attention to effectiveness. An example of this type of attacks was a campaign recorded in 2024, in which messages were sent to recipients in Poland in Kazakh, which did not fit into any Polish context. This group was also responsible for a disinformation campaign from the end of 2024, in which false threats were sent to plant explosives on government buildings in Poland and Ukraine (as Fire Cells Group). It was a psychological operation intended to cause panic, not an actual attack.
Malware
The CSIRT GOV team analyzed over 15,000 files reported by entities in the national cybersecurity system, 650 of which were deemed malicious. The dominant categories among the analyzed malware samples in 2024 were HTML Phisher, Snake Keylogger, Formbook, and Remcos. HTML Phisher is used in phishing attacks. This type of software is most often distributed by sending victims spoofed emails containing HTML/HTM attachments. After opening the attachment, the user sees a page imitating the service (e.g., online banking or an email login panel). The page is designed to closely resemble the original website. An HTML Phisher attack is also dangerous because it is often able to bypass spam filters and can operate partially offline, as it is opened locally on the victim’s device. Snake Keylogger is software that records all keyboard input by the user. Of course, this also includes login credentials. Snake Keylogger is often distributed via malicious email attachments or as part of a bundle with other software. Once installed, it runs in the background and is often able to evade detection by standard antivirus programs.
Formbook is a popular infostealer malware that focuses on stealing user data, such as login credentials, files, and information stored in web browsers (e.g., saved passwords and cookies). Formbook is sold, among other things, as malware -as-a-service, making it easily accessible to cybercriminals. It is primarily distributed via infected attachments (e.g., PDF files, Office documents) or links in phishing emails. Once a computer is infected, Formbook saves data in hidden files and uploads it to attacker-controlled servers. This type of malware supports functions such as keylogging, taking screenshots, and downloading and executing additional files sent by the attacker. Another malware family is Remcos. Remcos is a remote administration tool that can be used to gain complete control over an infected system. This software allows it to perform a range of actions, such as keylogging, screenshots, webcam and microphone monitoring, and even run arbitrary programs and commands on the victim’s computer. Remcos was initially promoted as a legitimate computer management tool, but quickly became a popular tool used by cybercriminal groups. It is most commonly distributed through phishing campaigns, where victims are tricked into opening infected attachments. Its features include the ability to run in stealth mode, making it difficult for standard security systems to detect.
ARAKIS GOV
The ARAKIS GOV system, mentioned earlier, is included separately in the statistics for a reason. The system’s primary purpose is to detect and automatically describe threats occurring in IT networks based on the aggregation, analysis, and correlation of data from various sources. In 2024, the system generated 5,446,734 alerts, including 3,322,068 with urgent priority, meaning they required an immediate response from administrators. A small percentage of alerts were high and medium priority, while nearly 40% were low priority, meaning they were purely informational alerts regarding the current situation at the interface between the internal network and the internet. Each recorded alert has precise technical data allowing for its verification and is classified in detail by the system. 56.60% of alerts were type 1 (communication to malicious addresses). These alerts resulted from attempts to establish communication with IP addresses or domains deemed malicious or potentially posing a threat.
Safety Assessment Summary
One of the tasks carried out by the CSIRT GOV Team is to assess the security of government administration institutions’ information and communication systems and critical infrastructure. In 2024, in accordance with the plan adopted for this year, assessments were conducted at 14 institutions, assessing a total of 64 network/IT system segments and 26 domains/subdomains and websites. As part of the security assessments, the CSIRT GOV Team conducted a series of tests to identify significant vulnerabilities affecting the security of the assessed entities’ information and communication infrastructure. These tests included passive and active data collection, identifying vulnerabilities in the architecture of network systems and services, web applications, exploiting vulnerabilities, and analyzing the impact of social engineering. As a result of the security assessments, the CSIRT GOV Team identified a range of vulnerabilities, ranging from low to critical. Critical and high threats were identified as the most important groups of vulnerabilities. These vulnerabilities included, for example: outdated software versions present in a number of systems and services used by entities, primarily concerning Apache HTTP Server, OpenSSL, VMware, use of unsupported software versions (Microsoft Windows 2008 R2 std . – end of support January 14, 2020, Microsoft SQL Server 2008 R2 – end of support July 9, 2019, VMware 6.7.x – end of support November 15, 2023), anonymous access, without required authentication or based on default passwords, etc.
Security Assessment – Examples of detected vulnerabilities:
1. Unsecured access to the Docker API – Access equivalent to accessing the server as a user with the highest privileges – root.
2. Discovery of the primary domain administrator’s credentials on the sysvol share.
3. High-privilege MSSQL user – As a result of a Password Spraying attack, access was gained to a network share containing the source code of a web application. A configuration file containing the credentials of the MSSQL service user was found within the code structure. During reconnaissance of the database engine using the compromised credentials, it was discovered that this user had high privileges, allowing them to reconfigure the database server. This was used to execute commands directly on the operating system.
4. Credential disclosure through fuzzing and directory listing: The HP Web Jetadmin service version 10.5.114213 (10.5 SR1) was detected on port 8085/tcp. As a result of the fuzzing tools (wfuzz), unsecure access to the log directory was detected. By enabling the Directory listing option, it was possible to quickly identify resources in a given path and proceed directly to further analysis and attacks on subsequent resources.
5. RCE – Java DebugWireProtocol (JDWP): Java DebugWireProtocol (JDWP) is a protocol used for communication between the debugger and the Java virtual machine. It does not use any authentication and can be exploited to execute remote commands (Remote Code Execution, RCE).
6. Cross-Site Scripting (XSS): By sending a POST request to https://[redacted]/4ses/servlet/
MainServlet?wbts:page=core.search.results.list, it was possible to inject JavaScript code into the search_text parameter. The lack of server-side validation caused the injected code returned in the HTTP response to be executed by the victim’s browser (Reflected XSS).
7. Sensitive data was included in the application logs.
8. DEBUG mode was enabled in the production application.
To properly protect an organization against incidents related to supply chain attacks (depending on the type of cooperation between entities), appropriate security measures may include:
● Risk assessment – a process aimed at identifying, assessing, and managing risks in the existing supply chain, as well as its new/potential connections;
● Regular audits and inspections – tasks confirming or denying the supplier’s ability to safely perform contractual activities;
● Controlling necessary authorizations – an activity involving regular verification of granted resource authorizations, solely on the basis of the so-called Least Privilege;
● Business continuity planning – developing business continuity plans and mitigating the effects of an incident should it occur;
● Data encryption – encrypting data during transmission and storage to ensure its proper security;
● Continuous monitoring – the use of threat and incident monitoring and reporting systems to ensure prompt action;
● Selection of suppliers who meet standards, such as those developed by the International Organization for Standardization (ISO).
